Connection
Responsibility for user authentication is delegated to an authentication service that is separate from the applications. This way of proceeding ensures great flexibility when integrating our applications into the environments where they will be deployed. Authentication services can be an Active Directory Federation Service domain, a dedicated application using Windows Identity Foundation, or a Google, Facebook or Hotmail authentication service. The applications remain responsible for assigning access and action rights using the federated services of the « Cyberjustice Core Services ».
The authentication process begins when the user accesses the application’s Internet site and requests to open a session. The user is then directed to the application responsible for verifying his or her identity. In the simplest version of this process, such as when only one provider is recognized, the process is direct. If more than one identity provider is available, the federated identity provider service may be responsible for directing the user to the right identity provider in accordance with a process to be established.
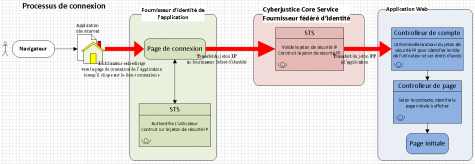
Once the user has input his or her user name and password, the identity provider verifies the information. If it is correct, the identity provider issues a security token containing information on the user. The browser transmits the token to the federated identity provider, and the service then validates the token. If it is valid, the service issues a new security token, which is an enhanced version of the preceding one. The purpose of this processing is to add to the token components providing the user’s authorizations. This will later make it possible for the application and « Cyberjustice Core Services » to verify the user’s authorizations. The new token is then transmitted to the application itself, and it can open a session for the user.
This content has been updated on 01/11/2016 at 13 h 58 min.
